Since 2022 Stimson’s Cyber Program has been researching and promoting cyber accountability, recognizing the gap between policy and practice. Past efforts have considered lessons from non-cyber domains and explored the implications for global cyber governance and for deterring harmful cyber activity. While political will is always a factor in accountability, so too is the capacity to keep systems secure and resilient. A major finding from Stimson’s earlier research on accountability is that cyber capacity-building is foundational for all aspects of cyber security and resilience, and therefore has a role in accountability, especially positive accountability and developing the policies and capabilities required for deterrence.
This was the impetus for a recent capacity-building workshop convened by Stimson’s Cyber Program in partnership with ICT4Peace and supported by Global Affairs Canada. The 2.5 day workshop included representatives from the governments of Cambodia, Lao, Philippines, Thailand and Vietnam spanning ministries of foreign affairs to technical agencies and national security and invited diverse experts from across the Indo-Pacific region. The workshop was held under the Chatham House Rule to foster candid exchange.
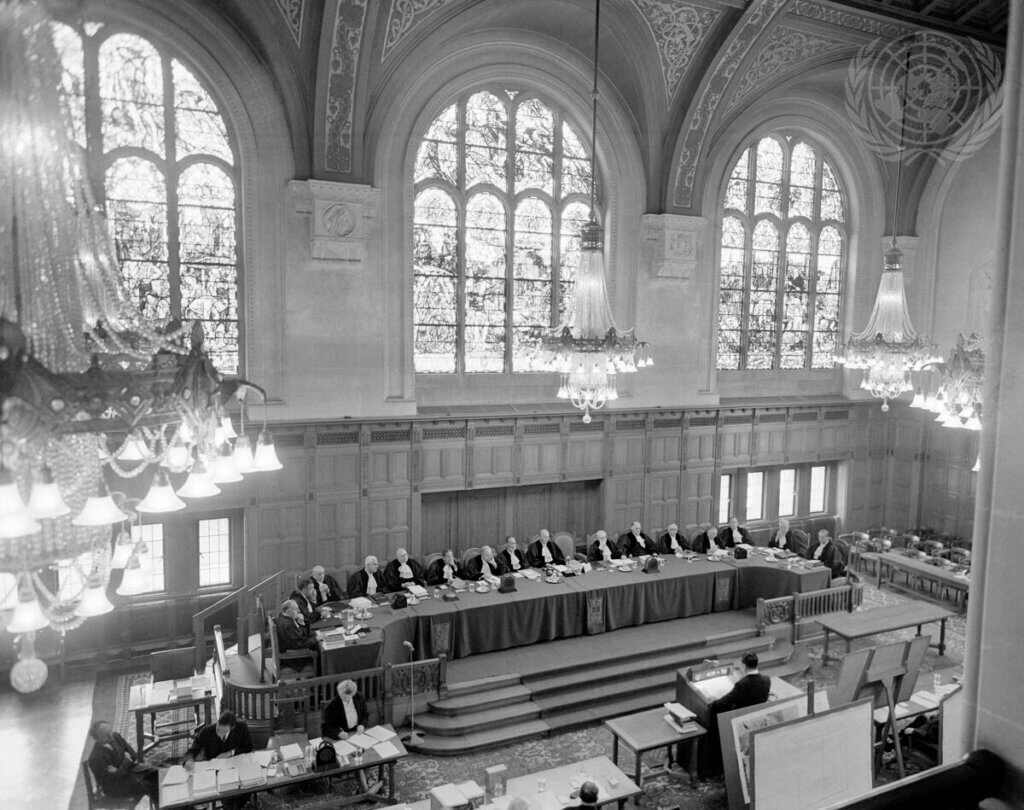
The workshop expanded on Stimson’s earlier work by zooming into the unique context and contours of Southeast Asia. In discussing international law, norms, attribution, deterrence, and responsible technology use, the training could assess real gaps – and progress – against some commonly employed tools for building accountability. Such tools include national interpretations of international law; national cybersecurity strategies and related legislation or regulation, including for cybercrime; information and intelligence sharing between domestic agencies as well as between countries; and recent tools developed by ASEAN, notably the 2024 Norms Checklist. Cyber Program Director Allison Pytlak and Fellow James Siebens were on the ground in Bangkok. CEO Brian Finlay and Chief of Staff Julian Mueller-Kaler were present for the opening session.
Highlights
- During the legal segment, experts examined complex questions of principles such as sovereignty, non-intervention and use of force. Of particular interest was Thailand’s forthcoming national position on these issues, scheduled for release in July. Their presentation detailed the collaborative drafting process and the strategic considerations influencing their approach. A growing number of states are releasing national statements on international law in relation to cyber capabilities, as a way to demonstrate their commitment to international law in cyberspace.
- The norms discussion session was predicated on the 11 non-binding UN cyber norms. Through interactive exercises, participants identified how these aspirational norms face practical challenges in operationalization. Many noted the absence of formal legal frameworks or regulatory policies in their countries, with geopolitical realities and coordination challenges also a factor. Human rights considerations were identified as indirect but important contributing factors to norm implementation.
- The session on national attribution frameworks reflected the complex geopolitical realities of Southeast Asia, where countries are carefully balancing security concerns with diplomatic relationships in their cybersecurity strategies. There is a greater tendency towards private or diplomatic, backchannel attribution, or to request a suspected perpetrator to assist in stopping attacks emanating from its territory, rather than assigning blame. Canada’s presentation of its national process for attributing responsibility for a cyber attack was a useful example and experts highlighted the distinction between technical, legal and political attribution.
- Another session sought to unpack the policy requirements of a cyber deterrence strategy, and to distinguish how deterrence applies in the cyber domain from how it is often discussed or utilized in non-cyber domains. The discussion revealed insights about prevailing attitudes and perspectives on cyber deterrence and emphasized the need for greater coordination between legal and technical mechanisms, as well as the benefits of deeper or additional regional cooperation, especially on threat monitoring, attribution, and sanctions.
- The workshop addressed the critical intersection of responsible technology use and human rights, featuring ICT4Peace’s new Comprehensive Toolkit for Responsible Technology Use—a practical resource helping companies balance security imperatives with human rights obligations. Gender gaps in cyber diplomacy and cybersecurity fields were also discussed.
The workshop culminated in a scenario-based discussion in which participants were asked to apply what they have learned about legal principles and norms as well as steps and considerations for deterrence and attribution to a fictional cyber incident affecting the region.
The conversation doesn’t stop in Bangkok – April’s convening was the first step in a longer path towards continued engagement with participating states, and towards a new Stimson Center report about regional approaches to cyber accountability planned for later this year.









Current Geopolitics Shift Deep-Sea Mining Debates