Editor’s Note: This case study was written by Debra Decker with extensive input from Nonresident Fellow Kathryn Rauhut, Darren Pain of the Geneva Association, and other sources who wish to remain anonymous, including from major insurance brokerages.
By Allison Pytlak, Senior Fellow and Director, Cyber Program
Security threats posed by the internet, artificial intelligence (AI), and quantum computing are multiplying at a speed with which governments and legislatures cannot possibly keep pace. Currently, market mechanisms such as credit ratings, product and service security ratings, liability adjustments, procurement requirements, tax adjustments, grants, and insurance are relatively untapped incentives that can play a pivotal role in promoting accountability for securing cyberspace. Market incentives to promote cybersecurity would help build a case that shifts security from a burdensome requirement or regulation to a value-added effort. Broadly speaking, market mechanisms are in different stages—some require more capacity or development, while others are evolving on their own terms.
One market incentive that could benefit from more coordinated support and integration into policy discussions is insurance. The industry’s effect on cybersecurity is not fully appreciated, and the accountability required of the insured and of the insurance industry is not yet well leveraged.
Although much has already been written about cyber insurance in relation to cyber issues within international relations, this case study considers cyber accountability from multiple perspectives to consider how collaborative public-private approaches can leverage commercial insurance to help better manage global cyber risks. Insurance is a mechanism the insureds use to transfer and share risks they do not want to carry themselves. Insurers hold the insured to account for certain behaviors as a condition of coverage and price their premiums based partly on the underwriters’ assessments of risks. Insurers are likewise held to account for their performance in cyberspace by their owners who provide the capital, by governments, and by the public who consider the societal effects of insurers’ actions, such as their role in ransomware claims.1Note that there are different types of insurance companies, including publicly traded insurers, mutual insurers that are owned by their policyholders, and others. These companies are regulated in different ways internationally. Underwriters help assess the risks these companies take on. Government regulations, liability considerations, and broader enterprise risk concerns within the insurance ecosystem all affect the industry and can be leveraged to improve cybersecurity.
Insurance as a Mechanism for Developing and Enforcing Norms for Commercial Coverage
Property and casualty insurance are the two main classes of commercial insurance.2“Commercial Insurance : Information,” Insurance Information Institute, https ://www.iii.org/publications/commercial-insurance/introduction. Property insurance covers business losses ranging from natural hazards to criminal acts, with losses relating not just to the property itself but also to losses from disruptions in business continuity.3Note that insurance does not cover the criminal acts of the policyholders themselves. Casualty insurance covers losses related to an individual’s or business’s legal liability, such as others’ losses from business products, operations, or property. Outside of these larger classes of insurance exist specialty insurance policies, such as professional liability and errors and omissions (E&O) to cover claims against a company for negligent performance. Cyber insurance is found within this class of specialty insurance. Many property and casualty policies have been “silent” on cyber risks, making it unclear what was covered. To address this problem, a special class of cyber insurance policies has been developed as a carve-out from other policies.4These “affirmative cyber insurance policies” can be stand-alone policies or included as specific endorsements to existing property and casualty (P&C) policies and evolved from initially focusing on third-party liability (harms to others) to first-party losses (harms suffered by the insured and cover losses to self).
Cyber insurance is intended to indemnify organizations for expenses and financial losses associated with “security incidents” and “privacy events,” as defined in the terms of the policies. A vast amount of coverage types is potentially available under most cyber insurance policies, such as for business continuity, but some cyber risks may not be addressed via a cyber policy. The associated risks typically not covered under cyber policies would be for losses such as general property damage, bodily injury, product recall, environmental impacts, etc.5See, for example: Kimberlee Leonard, “Understanding Data Breach vs. Cyber Liability Insurance,” business.com, February 22, 2024, https://www.business.com/insurance/data-breach/. Cyber insurance is not yet as uniform as other property and casualty insurance, so businesses rely on the expertise of specialized cyber insurance brokers to determine the most appropriate policies and terms for their needs. The cyber insurance market is the fastest growing area of insurance, with an estimated $12-13 billion in premiums in 2022 but expected to grow annually by 25-30%.6Manuel Adam, , et al., “Global Cyber Insurance: Reinsurance Remains Key To Growth,” S&P Global, August 29, 2023, https://www.spglobal.com/ratings/en/research/articles/230829-global-cyber-insurance-reinsurance-remains-key-to-growth-12813411; and “Cyber Insurance Market,” Hardware & Software IT Services: Fortune Business Insights, Report ID: FBI106287, last updated May 6, 2024, https://www.fortunebusinessinsights.com/cyber-insurance-market-106287.
Insurance Can Drive Accountability for Insureds’ Good Standards of Performance
The insurance industry has evolved over the years from when security professionals accompanied underwriters on client sites to help assess security, to clients completing long questionnaire-based cyber assessments, to today’s more streamlined assessments of management controls. Through these assessments, insurance can drive norms of behavior for those insured—but it is complex!
Prospective policyholders now complete an insurance application that typically includes questions regarding network protections, access management such as multifactor authentication, backup solutions, employee awareness, and privacy governance, among other considerations. Marsh, the world’s largest insurance broker, developed an assessment tool based on claims data and extensive client questionnaires to identify a potential insured’s actions that effectively reduce cyber risks.7Manuel Adam, , et al., “Global Cyber Insurance: Reinsurance Remains Key To Growth,” S&P Global, August 29, 2023, https://www.spglobal.com/ratings/en/research/articles/230829-global-cyber-insurance-reinsurance-remains-key-to-growth-12813411; and “Cyber Insurance Market,” Hardware & Software IT Services: Fortune Business Insights, Report ID: FBI106287, last updated May 6, 2024, https://www.fortunebusinessinsights.com/cyber-insurance-market-106287.This tool identified key controls,8Twelve key controls were developed—with one added for manufacturers and their operational technology, Marsh, “Cyber resilience: Twelve key controls to strengthen your security,” April 2022, https://www.marsh.com/es/en/services/cyber-risk/insights/cyber-resilience-twelve-key-controls-to-strengthen-your-security.html. which map to the US NIST Cybersecurity Framework and can define an entity’s cybersecurity “tier” that represents the strength of its risk controls.9“The NIST Cybersecurity Framework (CSF) 2.0,” U.S. Department of Commerce, National Institute of Standards and Technology, February 26, 2024, https://nvlpubs.nist.gov/nistpubs/CSWP/NIST.CSWP.29.pdf. Other certification and measurement schemes are also taken into account, such as Cybersecurity Capability Maturity Model, ISO 27000 series, European Union (EU) digital requirements, and individual states’ models.10“Cybersecurity Capability Maturity Model (C2M2),” Office of Cybersecurity, Energy Security, and Emergency Response, https://www.energy.gov/ceser/cybersecurity-capability-maturity-model-c2m2; that source can be cross-referenced to the NIST Framework: “Cybersecurity Capability Maturity Model to NIST Cybersecurity Framework Mapping,” NIST: National Cybersecurity Center of Excellence, https://www.nccoe.nist.gov/news-insights/cybersecurity-capability-maturity-model-nist-cybersecurity-framework-mapping; “An Introduction to ISO 27001, ISO 27002….ISO 27008,” The ISO 27000 Directory, https://www.27000.org/index.htm; Enisa, “Standards,” https://www.enisa.europa.eu/topics/standards; and “About Cyber Essentials,” National Cyber Security Centre, https://www.ncsc.gov.uk/cyberessentials/overview. In some cases, independent evaluators certify performance. Thus, in applying for cyber coverage, entities represent their performance and attest to their cybersecurity controls, their governance and compliance efforts around data privacy, and certain cyber hygiene behaviors that underwriters, who specialize in risk assessment, evaluate for coverage.
Cyber policy premiums can vary widely, but the inconsistency of coverage terms and conditions across insurers requires the prospective insured to use a decision matrix that includes consideration of premium, coverage terms, retention/deductible levels, and the total limit of coverage — all desired factors to determine the most appropriate cyber insurance program. Given the generally modest insurance policy limits today, larger companies with higher risk exposures typically have to build up their desired cyber coverage using multiple insurers. Other factors often considered when choosing insurance coverage include whether the company has other covers with an insurer, what level of flexibility a company would like around selection of third-party cyber incident vendors (such as forensic specialists and other firms), and the insurer’s domicile (U.S., Great Britain, Bermuda, or other domestic markets for foreign-domiciled entities). For the insurance company, premium pricing is a function of the deductible levels in the policy, its limits of coverage in dollar terms, and the policy wordings and exclusions. Premiums can vary among insurers for the same entity based on the insurer’s own risk appetite for that industry class, its larger relationship with the insured who may have other coverages with the insurer, the competition in the market from other insurers, and the insurer’s ability to earn investment income on the premiums it sets aside to cover future expected claims.
Not all organizations obtain cyber coverage. Some retain cyber risks. Others may set up captive insurers to manage their risks or establish risk pools with those in their industry, such as via the new MIRIS pool in Europe or in the civil nuclear industry.11“Mutual Insurance and Reinsurance for Information Systems,” Miris, https://www.miris-insurance.com/en; and Éireann Leverett, “Cyber Insurance for Civil Nuclear Facilities Risks and Opportunities,” Chatham House, May 8, 2019, updated December 7, 2020, https://www.chathamhouse.org/2019/05/cyber-insurance-civil-nuclear-facilities. While some organizations may not see the value of cyber insurance given current policy terms, the insurance industry is evolving to provide new services alongside indemnifying policyholders’ losses and will likely attract more prospective clients to the already growing cyber insurance market. Brokers and insurers are increasingly providing wraparound services to help organizations not only reduce their vulnerability but also prepare for and be resilient to any future cyber incident.12Marion Rae, “‘Active cyber insurers to combat scourge of ransomware,” The West Australian, November 5, 2023,https://thewest.com.au/business/active-cyber-insurers-to-combat-scourge-of-ransomware-c-12453662. For example, Marsh reorganized in 2024 to provide more integrated services,13“Marsh to launch global cyber practice; appoints new leaders,” Marsh, 24 October 2023, https://www.marsh.com/us/about/media/tom-reagan-named-global-specialty-head-of-cyber.html. and its brokers can also help explain some of the technical aspects of coverage.14Marsh, “Setting the Record Straight on Cyber Insurance,” https://www.marsh.com/ca/en/services/cyber-risk/insights/setting-record-straight-on-cyber-insurance.html. New entrants into the market include firms like Microsoft and Amazon that partner with insurers to provide coverage as well as monitoring services, threat information, and risk management advice.15“Anatomy of a modern attack surface: Six areas for organizations to manage,” Microsoft, May 2023, https://www.microsoft.com/en-us/security/business/security-insider/threat-briefs/anatomy-of-a-modern-attack-surface/; and “AWS Cyber Insurance Competency Partners,” AWS,https://aws.amazon.com/partners/cyber-insurance-partner-solutions/.
An important aspect of insurers holding policyholders accountable is an entity’s application, as it becomes an attestation of performance. If a policyholder company attests to having certain standards of performance that it does not actually possess, the insurance coverage may be void. The insurance industry recognizes that it needs to better understand what norms work to reduce cyber risks so that it can price policies more accurately, establish more effective norms as requirements of coverage, and help individual insurers better assess their exposure to risks. Swiss Re Institute and the AXA Research Fund, research entities established by two leading re/insurers, are jointly supporting independent research to this end with a focus on resilience to systemic risks, a topic discussed later in this paper.16“Joint Risk Resilience Partnership: Funding Research on Systemic Risks,” Swiss Re Institute, https://www.swissre.com/institute/partnerships/joint-risk-resilience-initiative.html.
Insurance May Help Drive Better Accountability Over Tech Providers
Technology providers include providers of hardware, software and managed services, known as managed service providers (MSP). They represent special cases for insurers. Insurers may cover losses arising from claims by other insureds using their products and services and for insurance coverage contracted with these providers/managers for professional indemnity, often in the form of professional liability as well as errors and omissions (E&O) insurance.17For an explanation of professional indemnity and errors and omissions (E&O) coverage, see: “Clearing up the differences between E&O and PI,” ANZIIF, September 20, 2022, https://anziif.com/professional-development/articles/2022/09/clearing-up-the-differences-between-eo-and-pi. These technology providers/managers are critical components of the supply chain and pose significant risks across client groups due to their vulnerabilities/poor performance and thus to insurers, who fear “risk aggregation” and systemic risks such as evidenced in SolarWinds, MS Exchange, and Change Healthcare incidents.18See, for example: Joey Sylvester, “Two Years Later: An Analysis of SolarWinds and the Impact on the Cyber Insurance Industry,” Gallagher, https://www.ajg.com/us/news-and-insights/2022/aug/two-years-later-an-analysis-of-solarwinds-and-the-impact-on-the-cyber-insurance-industry.
Since it is difficult today to assess the quality of some hardware, software, or MSPs, this challenge means insurers cannot easily consider their quality in their insurance contracts both for their liability coverage and for the cyber coverage of the entities using their tech products/services. Insurance requirements alone could not, in any case, drive better, more secure services from these entities. Tech providers already protect themselves from liability and performance claims through expressed limitations on liabilities in sales agreements, licensing exclusions, and bespoke MSP service agreements. However, there is a trend toward clarity about the responsibilities and prospective liabilities of these tech industries that may drive more performance claims against tech providers/managers and might drive more of them to insure for their errors and omissions.19Anastasia B., “How Do You Limit Liability as an MSP?” MSP360, September 15, 2020, https://www.msp360.com/resources/blog/how-msps-can-limit-liability/. In late 2023, a notable class action lawsuit was filed against U.S. tech company Intel for security issues in its central processing units (CPUs) and its remediation actions that slowed computer performance.20Eduard Kovacs, “Intel Sued Over ‘Downfall’ CPU Vulnerability,” Security Network: Endpoint Security, November 10, 2023, https://www.securityweek.com/lawsuit-filed-against-intel-over-downfall-cpu-vulnerability/. Nonetheless, cautions are needed as insurance itself could become a moral hazard if risks are not appropriately shared and priced in order to move the tech providers toward more secure design/performance rather than assumptions of liability coverage for poor security.
The potential for litigation, fines, and reputational harm may increase as governments express heightened requirements for the IT industry’s performance. U.S. President Biden’s 2023 cybersecurity strategy calls to “reshape laws that govern liability for data losses and harm caused by cybersecurity errors, software vulnerabilities, and other risks created by software and digital technologies.”21“National Cybersecurity Strategy,” (Washington: The White House, March 2023), https://www.whitehouse.gov/wp-content/uploads/2023/03/National-Cybersecurity-Strategy-2023.pdf. The EU has adopted a voluntary certification scheme and some mandatory security requirements for hardware and software products.22“First EU-wide cybersecurity certification scheme to make European digital space safer,” European Commission, January 31, 2024, https://digital-strategy.ec.europa.eu/en/news/first-eu-wide-cybersecurity-certification-scheme-make-european-digital-space-safer; Mark Young and Aleksander Aleksiev, “The EU’s Cyber Resilience Act Has Now Been Agreed,” Convington: Inside Privacy, December 1, 2023,https://www.insideprivacy.com/cybersecurity-2/the-eus-cyber-resilience-act-has-now-been-agreed/; and “Europe agrees on rules to protect smart devices from cyber threats,” Business Insurance, December 1, 2023, https://www.businessinsurance.com/article/20231201/NEWS06/912361339/Europe-EU-agrees-on-rules-to-protect-smart-devices-from-cyber-threats. The World Economic Forum has called for international certification schemes.23“International Cybersecurity Certification Framework: Pathways to Collaboration and Situational Analysis,” Global Economic Forum, September 2021, https://www3.weforum.org/docs/WEF_GFC_Cybersecurity_International_Certification_Framework_2021.pdf Industry security will increase, but users’ security expectations will also rise. Thus, deviations from these regulatory or best-practice performances that result in user harms may well lead to increased, more substantiated claims; and insurers will be involved in covering some of the tech providers’ related costs through the providers’ own professional liability policies. Some NGOs such as Atlantic Council had already been calling for more explicit standards of care for tech providers so that the judicial system can be leveraged to reduce risks.24Trey Herr, Robert Morgus, Stewart Scott, and Tianjiu Zuo, “Buying down risk: Cyber liability,” Atlantic Council, May 3, 2022, https://www.atlanticcouncil.org/content-series/buying-down-risk/cyber-liability/.
In sum, insurers have an interest in encouraging progress to establish agreed standards of secure development for software, adopt security by design standards, and promote safe havens from legal liability for those who abide by best practices to meet cybersecurity standards, like those that the US SAFETY Act provides to entities that have certified good practices.25The US SAFETY Act provides limitations on the liability of entities for products, systems, and services, such as providing security at a football game, for those that receive certification. See: “Safety Act,” Homeland Security, https://safetyact.gov/. All of these good practices can increase security and protect tech providers and thereby insurers of those providers from losses. Once good practices are identified and become norms, regulations, or laws, insurers can better assess their carried risks and review and appropriately structure policy conditions based on performance of hardware, software, and service providers—or can deny coverage.
Issues of tech companies’ liability for security and their insurance coverage have arisen already, including in 2017 with the Wanna Cry exploit, a ransomware cyberworm that infected unpatched Microsoft operating systems.26For a look into wider issues of liability for that vulnerability and the government stockpiling of exploits, see: Jan Wolfe, “Cyber attack could spark lawsuits but not against Microsoft,” Reuters, May 16, 2017,https://www.reuters.com/article/us-cyber-attack-liability-idUSKCN18B2SE/; and Chappell, Bill, “WannaCry Ransomware: Microsoft Calls Out NSA For ‘Stockpiling’ Vulnerabilities ,” NPR, May 15, 2017, https://www.npr.org/sections/thetwo-way/2017/05/15/528439968/wannacry-ransomware-microsoft-calls-out-nsa-for-stockpiling-vulnerabilities. Insurers’ engagement should lead them to have an interest in prompting all commercial entities to maintain a Software Bill of Materials (SBOM) in their IT system so that they can add identify elements in their systems, address vulnerabilities, and ensure updated systems. Requiring SBOMs would also present a way for insurers to understand their aggregated portfolio exposure to a given technology and to defend their insured tech companies from performance violations that tech customers allege. This symbiotic relationship of risk identification and management among the insured customers on both sides of the tech relationship, that is the tech providers and users, may be hard to institute today given all the information required to be stored and assessed and the many nuances of threats, vulnerabilities, responses and behaviors that need to be factored into an assessment. In the future, big data and AI could well help support this approach and drive more public-private as well as private-private partnerships in data and experience sharing.27Derek Johnson, “Software liability: The hard truths of holding manufacturers responsible,” SC Media, May 30, 2023, https://www.scmagazine.com/analysis/software-liability-the-hard-truths-of-holding-manufacturers-responsible. The good news is that the insurance industry is already being innovative in using AI and in developing AI insurance solutions for AI developers and users.28“Innovative coverage for Artificial Intelligence solutions,” Munich RE: Insure AI, https://www.munichre.com/en/solutions/for-industry-clients/insure-ai.html.
Insurers’ Need to Help Address Ransomware
The insurance industry has been criticized for paying when ransomware strikes their clients. However, Marsh notes the payment of ransomware is a customer decision and attackers do not necessarily seek out those who are insured.29Marsh, “Cyber Insurance is Supporting the Fight Against Ransomware,” https://www.marsh.com/ca/en/services/cyber-risk/insights/cyber-insurance-supporting-fight-against-ransomware.html. The insurance broker also notes that, although ransom attacks have increased, payouts as a percentage of attacks have declined largely due to the enhanced controls, such as strong backup protocols, that insureds are now being required to have to qualify for coverage. Nonetheless, hackers can infiltrate, and have infiltrated according to one industry source, companies’ systems to find details of the target’s insurance policies. Royal United Services Institute (RUSI), a London-based think tank, did a yearlong study of ransomware payouts and their relationship to cyber insurance. Published in 2023, RUSI’s study found “no compelling evidence that victims with cyber insurance are much more likely to pay ransoms than those without.”30Jamie MacColl, et al., “Cyber Insurance and the Ransomware Challenge,” RUSI, July 31, 2023, https://www.rusi.org/explore-our-research/publications/occasional-papers/cyber-insurance-and-ransomware-challenge. However, the study noted the need to have better ransomware reporting to authorities, which insurers could require of policyholders, and recommended, among other things, that insurers work to develop and identify best practices in ransomware responses and seek the possible development and use of specialist ransomware response firms.
The U.S. Counter Ransomware Initiative at its November 2023 meeting rightly committed the participating states to closer engagement with the insurance industry on addressing ransomware and to the encouragement of ransomware reporting.31“International Counter Ransomware Initiative 2023 Joint Statement,” The White House, November 1, 2023, https://www.whitehouse.gov/briefing-room/statements-releases/2023/11/01/international-counter-ransomware-initiative-2023-joint-statement/ In an innovative move, France amended its laws to allow ransomware payouts under insurance only to entities that have informed authorities of an incident within 72 hours.32“French Law Authorizes Insurability of ‘Cyber-Ransoms’ Paid by Victims, Subject to Prompt Filing of Complaint,” Jones Day, February 2023, https://www.jonesday.com/en/insights/2023/02/french-law-authorizes-insurability-of-cyberransoms-paid-by-victims; and Stéphanie Faber and Charles Helleputte, “To Benefit from Insurance Coverage in France Businesses Must File a Complaint Within 72 Hours of a Cyberattack,” Privacy World, March 1, 2023, https://www.privacyworld.blog/2023/03/to-benefit-from-an-insurance-coverage-in-france-businesses-must-file-a-complaint-within-72-hours-of-a-cyberattack/ As the U.S. moves toward some required reporting of ransomware, it is relaunching its Cybersecurity Insurance and Data Analysis Working Group (CIDAWG) to help identify ways to “drive down cyber risks” and to work at this effort collectively.33Nitin Natarajan, “Cybersecurity Insurance and Data Analysis Working Group Re-Envisioned to Help Drive Down Cyber Risk,” CISA, November 20, 2023, https://www.cisa.gov/news-events/news/cybersecurity-insurance-and-data-analysis-working-group-re-envisioned-help-drive-down-cyber-risk. In the United States, proposed rules for critical infrastructure reporting of incidents, including ransomware, are open for comment through July 2024.34Department of Homeland Security, “Cyber Incident Reporting for Critical Infrastructure Act (CIRCIA) Reporting Requirements; Extension of Comment Period,” Federal Register, May 6, 2024, https://www.federalregister.gov/documents/2024/05/06/2024-09505/cyber-incident-reporting-for-critical-infrastructure-act-circia-reporting-requirements-extension-of. However, the issue of an outright ban for all on ransomware payments is not considered realistic.35Brian E. Finch, Aimee P. Ghosh, and Amaris Trozzo, “International Counter Ransomware Initiative Pledges to Halt Government Ransom Payments, but with Exceptions,” Pillsbury, November 2023, https://www.pillsburylaw.com/en/news-and-insights/international-counter-ransomware-initiative-government-ransom-payments.html; “New Ransomware Reporting Requirements Kick in as Victims Increasingly Avoid Paying,” Coverware, January 26, 2024, https://www.coveware.com/blog/2024/1/25/new-ransomware-reporting-requirements-kick-in-as-victims-increasingly-avoid-paying.
The issue from the insurance industry side is what companies or associations are best placed and willing to engage and to help drive needed changes across the industry.
Insurer’s Concerns Can Drive Work to Identify and Manage Systemic Risks and Keep the Industry Viable
Insurance is one of the biggest industries in the world.36“Global Biggest Industries by Revenue in 2024: The 10 Global Biggest Industries by Revenue,” Ibis World, https://www.ibisworld.com/global/industry-trends/biggest-industries-by-revenue/. For more applied research, see: “Joint Risk Resilience Partnership: Funding Research on Systemic Risks,” Swiss Re Institute, https://www.swissre.com/institute/partnerships/joint-risk-resilience-initiative.html; and “The Empirical Security Research Group,” Stanford, https://esrg.stanford.edu/. The Financial Stability Board (FSB), formalized during the 2008 financial crisis, promoted more standardization of financial regulation to include oversight of insurers to avoid future global financial shocks.37“History of the FSB,” Financial Stability Board, https://www.fsb.org/about/history-of-the-fsb/. Insurers often act as financial intermediaries, especially for some as poolers of risk in credit insurance. The review of insurers is suspended while the FSB considers how to better assess and oversee insurers who might fail and trigger global financial shocks. See FSB 2024 workplan here: “2023 Resolution Report: ‘Applying lessons learnt,’” FSB, December 15, 2023, https://www.fsb.org/wp-content/uploads/P151223.pdf; and the assessment methodology of regulatory frameworks for insurers here: “Key Attributes Assessment Methodology for the Insurance Sector,” FSB, August 25, 2020, https://www.fsb.org/2020/08/key-attributes-assessment-methodology-for-the-insurance-sector. Thus, maintaining a healthy insurance industry globally is important. The question is how to achieve this goal given the nascent understanding of current/emerging digital risks.
While insurers have long worried about being overexposed to an industry, region, or market change such as interest rates, those systematic risks differ from growing concerns over systemic risks.38Joseph Nguyen, “Systemic Risk vs. Systematic Risk: What’s the Difference?” Investopedia, February 26, 2024, https://www.investopedia.com/ask/answers/09/systemic-systematic-risk.asp. Systemic risks can have cascading and often unexpected or difficult effects to predict and assess due to connections among entities and systems—and can be complex or otherwise obfuscated from insurers’ view.39David Forscey, Jon Bateman, Nick Beecroft, and Beau Woods, “Systemic Cyber Risk: A Primer,” Carnegie Endowment for International Peace, March 7, 2022, https://carnegieendowment.org/research/2022/03/systemic-cyber-risk-a-primer?lang=en. These risks can be less known but are widely used, like the Log4j piece of open-source software that was found to have vulnerabilities.40“Log4j vulnerability—what everyone needs to know,” National Cyber Security Centre, https://www.ncsc.gov.uk/information/log4j-vulnerability-what-everyone-needs-to-know; and “The Key to Understanding Systemic Cyber Risk is Market Penetration,” Internet Security Alliance, October 26, 2023, https://isalliance.org/the-key-to-understanding-systemic-cyber-risk-is-market-penetration/. Systemic risks can also stem from catastrophic events, like an attack on the underlying structure of the internet or something more directed like the takedown of a financial payments system.41The insurance industry marketplace Lloyd’s estimated the loss of a major payment system to trigger $3.5 trillion in losses worldwide. See: “Lloyd’s systemic risk scenario reveals global economy exposed to $3.5 trillion from major cyber attack,” Lloyds, October 18, 2023, https://www.lloyds.com/about-lloyds/media-centre/press-releases/lloyds-systemic-risk-scenario-reveals-global-economy-exposed-to-3.5trn-from-major-cyber-attack. Now AI has become a concern for compounding malicious actors’ targeting abilities.42“The near-term impact of AI on the cyber threat,” National Cyber Security Centre, January 24, 2024, https://www.ncsc.gov.uk/report/impact-of-ai-on-cyber-threat; https://axaxl.com/fast-fast-forward/articles/2023-axa-future-risks-report. Some work is underway to help identify systemic risks, including funding from re/insurers (noted earlier),43“Joint Risk Resilience Partnership: Funding Research on Systemic Risks,” Swiss Re Institute, https://www.swissre.com/institute/partnerships/joint-risk-resilience-initiative.html; and “The Empirical Security Research Group,” Stanford, https://esrg.stanford.edu/. See also, “Paris Call: Protecting Critical Infrastructures Against Systemic Harms,” Paris Peace Forum, November 10, 2023, https://parispeaceforum.org/publications/paris-call-protecting-critical-infrastructures-against-systemic-harms/; “Systemic Cyber Risk Reduction,” CISA, https://www.cisa.gov/resources-tools/programs/systemic-cyber-risk-reduction; and Organization for Economic Cooperation and Development, “Conclusions and Recommendations”, in Emerging Risks in the 21st Century: An Agenda for Action, (Paris, OECD Publishing: 2003), https://www.oecd.org/sti/futures/globalprospects/37944611.pdf. the World Economic Forum being an important hub of research,44In 2016, Zurich Re/Insurance recommended the World Economic Forum (WEF) help build a lexicon and analyze systemic risks: “Understanding systemic cyber risk,” Zurich, November 25, 2016, https://www.zurich.com/en/knowledge/topics/digital-data-and-cyber/wef-understanding-systemic-cyber-risk. See, proposed lexicon and other work here: “Systemic Cybersecurity Risk and role of the Global Community: Managing the Unmanageable,” World Economic Forum, November 2022, https://www3.weforum.org/docs/WEF_GFC_Cybersecurity_2022.pdf; “Beneath the Surface: Technology-driven systemic risks and the continued need for innovation,” World Economic Forum, October 28, 2021, https://www.weforum.org/publications/beneath-the-surface-technology-driven-systemic-risks-and-the-continued-need-for-innovation/; and “Global Future Council on the Future of Cybersecurity,” World Economic Forum, https://www.weforum.org/communities/gfc-on-cybersecurity/. and the Carnegie Endowment for International Peace also working on systemic risks, insurance, and attribution.45Ariel Levite, Scott Kannry, and Wyatt Hoffman, “Addressing the Private Sector Cybersecurity Predicament: The Indispensable Role of Insurance,” Carnegie Endowment for International Peace, November 7, 2018. https://carnegieendowment.org/research/2018/11/addressing-the-private-sector-cybersecurity-predicament-the-indispensable-role-of-insurance?lang=en¢er=europe. See also: David Forscey, Jon Bateman, Nick Beecroft, and Beau Woods, “Systemic Cyber Risk: A Primer,” Carnegie, March 7, 2022; John Pendleton, Ariel (Eli) Levite, and Bob Kolasky, “Cloud Reassurance: A Framework to Enhance Resilience and Trust,” Carnegie, January 18, 2024, https://carnegieendowment.org/2024/01/18/cloud-reassurance-framework-to-enhance-resilience-and-trust-pub-91394; Ariel (Eli)Levite, Lu Chuanying, George Perkovich, and Fan Yang, “Managing U.S.-China Tensions Over Public Cyber Attribution,” Carnegie, March 28, 2022, https://carnegieendowment.org/2022/03/28/managing-u.s.-china-tensions-over-public-cyber-attribution-pub-86693. https://carnegieendowment.org/research/2022/03/systemic-cyber-risk-a-primer?lang=en; John Pendleton, Ariel (Eli) Levite, and Bob Kolasky, “Cloud Reassurance: A Framework to Enhance Resilience and Trust,” Carnegie, January 18, 2024, https://carnegieendowment.org/2024/01/18/cloud-reassurance-framework-to-enhance-resilience-and-trust-pub-91394; Ariel (Eli)Levite, Lu Chuanying, George Perkovich, and Fan Yang, “Managing U.S.-China Tensions Over Public Cyber Attribution,” Carnegie, March 28, 2022, https://carnegieendowment.org/2022/03/28/managing-u.s.-china-tensions-over-public-cyber-attribution-pub-86693.
Better risk modeling alone cannot address managing risk accumulation from cyber-related systemic events. This fact has limited the growth in affordable cyber coverage. The Geneva Association, an international association of insurance companies, noted in its comprehensive paper on cyber risks, “Insurers are employing stricter contract wording and maintaining low policy limits [in comparison to limits provided on other types of commercial insurance], but with potential cyber exposures only set to grow, this implies a huge and persistent protection gap.”46Darren Pain, “Cyber Risk Accumulation: Fully tackling the insurability challenge,” The Geneva Association, November 2023, https://www.genevaassociation.org/sites/default/files/2023-11/cyber_accumulation_report_91123.pdf.
Part of this gap had been due to reinsurers, to whom insurers lay off some risks, not being willing to take up some of those cyber exposures. That reality has been changing as insurers insist clients have better risk management and require tighter contract wording.47Ben Dyson, “Reinsurers warming to cyberrisk as market matures,” S&P Global, 5, October 2023, https://www.spglobal.com/marketintelligence/en/news-insights/latest-news-headlines/reinsurers-warming-to-cyberrisk-as-market-matures-77737466; Erica Davis, “Worst May be Over for Tough Cyber Reinsurance Market,” Marsh-McLennan, https://www.marshmclennan.com/insights/publications/2022/october/worst-may-be-over-for-tough-cyber-reinsurance-market.html. However, the tail risks—those low-probability but high-consequence events—persist and constrain primary as well as reinsurance policies.
One of those tail risks involves wars. The historic general insurance exclusion for “hostile” or “warlike acts” persisted in insurance policies until the 2017 NotPetya virus, which originally targeted Ukraine, spread to others and caused significant losses; that led to global claims under all-risk policies, as the attacks were attributed to Russia. Yearslong litigation ended in out-of-court settlements for two large claims by Merck (a pharmaceutical company) and Mondelez (one of the world’s largest snack food companies) and their insurers.48“Merck Settles Coverage Dispute with Insurers over War Exclusion in NotPetya Attack,” Insurance Journal, January 5, 2024, https://www.insurancejournal.com/news/national/2024/01/05/754582.htm. For more background, see: Allison Ebeck and Shelby Guilbert Jr., “Policyholders Beware—Lloyd’s is Adding New Exclusions to Limit Insurance Coverage for State-Sponsored Cyber Attacks Next Month—Are you Prepared?” JD Supra, February 23, 2023, https://www.jdsupra.com/legalnews/policyholders-beware-lloyd-s-is-adding-1690869/. Lloyds of London (a specialist insurance and reinsurance market) now requires all policies underwritten by its syndicates not to be silent on the potential cyber exposures covered and to state clearly whether policies affirm coverage for cyber incidents.49“Cyber war clauses,” Lloyd’s Market Association: Underwriting Team, https://www.lmalloyds.com/LMA/Underwriting/Non-Marine/Cyber_Clauses/cyber_war_clauses.aspx. Lloyd’s has required that all policies, including cyber policies, clearly and directly address how policies are to address events linked to sovereign states involved in wars, whether declared or not, or state-backed threat group activity.50Julian Miller, and Evans Toma, “War Exclusions in Cyber Policies: An Overview,” Dac Beachcroft, March 30, 2023, https://www.dacbeachcroft.com/en/What-we-think/war-exclusions-in-cyber-policies-an-overview; L.S. Howard, “Lloyd’s Cyber War Exclusions: Confusing, Disruptive, but Necessary?” Insurance Journal, May 9, 2023, https://www.insurancejournal.com/news/international/2023/05/09/720020.htm; “Cyber war clauses,” Lloyd’s Market Association. However, some have asked for more clarity on these definitions.
The U.S. government has been considering a risk-sharing scheme in which the federal government “backstops”—that is, provides funding support—against catastrophic losses, akin to the Terrorism Risk Insurance shared-risk model or the National Flood Insurance Program. The goal would be to broaden the availability and affordability of cyber reinsurance but without promoting moral hazard.51“Remarks by Assistant Secretary Graham Steele at the Federal Insurance Office and NYU Stern Volatility and Risk Institute Conference on Catastrophic Cyber Risk and a Potential Federal Insurance Response,” U.S. Department of the Treasury, November 17, 2023, https://home.treasury.gov/news/press-releases/jy1922. For a summary of stakeholder comments, see: Federal Insurance Office, “Summary of Comments on Request for Comment: Federal Insurance Response to Catastrophic Cyber Incidents: Presentation to the Federal Advisory Committee on Insurance,” U.S. Department of the Treasury, March 29, 2023, https://home.treasury.gov/system/files/311/2023-03-27%20Presentation%20Summary%20of%20Cat%20Cyber%20RFI%20Responses.pdf. Recent Treasury remarks: Chad Hemenway, “Federal Cyber Insurance Backstop Is Warranted With Focus on Catastrophic Risk,” Insurance Journal, November 28, 2023, https://www.insurancejournal.com/news/national/2023/11/28/749640.htm. For additional background, see: Mariam Baksh, “Agencies Push Deadline to Comment on Would-Be Federal Cyber Insurance Program,” NextGov, November 18, 2022, https://www.nextgov.com/cybersecurity/2022/11/agencies-push-deadline-comment-would-be-federal-cyber-insurance-program/379858/. For flood insurance, see: “Flood Insurance,” FEMA, https://www.fema.gov/flood-insurance.Indications are that the insurance market’s development, including through new mechanisms like insurance-linked securities (ILS),52“Catastrophe Bond (cat bond),” Artemis, October 12, 2015, https://www.artemis.bm/glossary/catastrophe-bond-cat-bond/.may well provide added market capacity to allow the industry to absorb more risks.53OECD, “The Role of Public Policy and Regulation in Encouraging Clarity in Cyber Insurance Coverage,” 2020, https://www.oecd.org/finance/insurance/The-Role-of-Public-Policy-and-Regulation-in-Encouraging-Clarity-in-Cyber-Insurance-Coverage.pdf. However, a wait-and-see approach chances a major cyber event occurring before the market—and its support for restoring business functions—has evolved sufficiently. Any government support program has an element of moral hazard in it, as does all insurance including ILSs.54Daniel Woods, “A Federal Cyber Insurance Backstop is Premature,” Lawfare, January 19, 2023, https://www.lawfaremedia.org/article/federal-cyber-insurance-backstop-premature; Tobias Götze, “Risk Transfer and Moral Hazard: An Examination on the Market for Insurance-Linked Securities,” Nanyang Business School Forum on Risk Management and Insurance: Nanyang Technological University, October 9, 2019, https://blogs.ntu.edu.sg/nbsfrmi/2018/10/09/risk-transfer-and-moral-hazard-an-examination-on-the-market-for-insurance-linked-securities-2/. However, the triggers and terms of both these mechanisms can help to manage the risks. For example, any backstop should consider being available only to re/insurers who require certain levels of security from those insured, thus helping to drive greater overall cybersecurity. In addition, rating agencies will become increasingly a focus as they give ratings that help drive the pricing of ILS; the question then becomes how well they are able to rate them.55Maren Josefs, et al., “Credit FAQ: How We Analyze Insurance-Linked Securities,” S&P Global, September 8, 2023, https://www.spglobal.com/ratings/en/research/articles/230908-credit-faq-how-we-analyze-insurance-linked-securities-12845073; “Insurance-Linked Securities Rating Criteria,” Fitch Ratings, June 16, 2023, https://www.fitchratings.com/research/insurance/insurance-linked-securities-rating-criteria-16-06-2023.
Key Takeaways and Recommendations
Strengthen Insurance as A Mechanism to Promote Accountability
Insurance is an important tool for promoting accountability in cyberspace but can be strengthened. Several efforts should be considered to support this objective. The plan within the Counter Ransomware Initiative to engage with insurers needs to be jump-started and expanded to both a public-private and private-private partnership. For example, a series of roundtable discussions of representative insurers, brokers, customers, and others could be held to address some of the outstanding insurance ideas and concerns.
Require and Standardize Incident Reporting and Processes for Better Risk Analysis and Management
Incident reporting is needed in a responsible manner and should be standardized to allow for better risk assessments and management by all stakeholders, including law enforcement. Efforts to require reporting are moving forward in a piecemeal fashion with many informal efforts to gather incident data, including in academia and from NGOs. Some states and organizations are requiring ransomware and other incident reporting that is not necessarily consistent even within a state.56Internal U.S. reporting requirements differ among sectors, see: David Simon, et al., “Federal Report Proposes Harmonization of Divergent Cyber Incident Reporting Regimes,” Skadden, October 16, 2023, https://www.skadden.com/insights/publications/2023/10/federal-report-proposes-harmonization. Certain subsectors require incident reporting, see: “Cyber Incident Notification requirements,” National Credit Union Administration, August 2023, https://ncua.gov/regulation-supervision/letters-credit-unions-other-guidance/cyber-incident-notification-requirements. The U.S. Securities and Exchange Commission now requires disclosure of incidents within four days for public companies that have material impact, see: Erik Gerding, “Cybersecurity Disclosure,” U.S. Securities and Exchange Commission, December 14, 2023, https://www.sec.gov/news/statement/gerding-cybersecurity-disclosure-20231214. See an early summary of SEC regulations in its press release: “SEC Adopts Rules on Cybersecurity Risk Management, Strategy, Governance, and Incident Disclosure by Public Companies,” U.S. Securities and Exchange Commission, 2023, https://www.sec.gov/news/press-release/2023-139. The EU is moving forward with many directives/regulations, see: “New Organizational Requirements,” NIS2 Directive: NIS2 Requirements, https://nis2directive.eu/nis2-requirements/.
The U.S. and other countries are requiring reporting of ransomware and other cyber incidents from certain entities such as critical infrastructure. There is sometimes a stigma when investors see systems as being vulnerable to cyber threats which leads to lower ratings or stock prices, or customer insecurity. Required reporting could help erase the stigma of vulnerable systems and lead to more effective monitoring of the threat landscape thereby benefiting all entities and law enforcement.57In 2023, the FBI reported that the internationally coordinated takedown of Hive, the ransomware-as-a-service platform, returned over $100 million to victims of ransomware and that, during the FBI’s monitoring of Hive, only 20% of entities had reported the ransoms to authorities. See: Toney Riley, “FBI seizes Hive ransomware group infrastructure after lurking in servers for months,” Cyberscoop, January 26, 2023, https://cyberscoop.com/fbi-europol-hive-ransomware-group/. It would also help insurers/academics/tech firms in their risk research to build better models for security protections. In the short term, the French approach of requiring confidential reporting to authorities of ransomware attacks as a prerequisite of insurance payout might be expanded internationally. A pilot program to expand and systematize such reporting could be developed working with appropriate stakeholders, possibly through the International Counter Ransomware Task Force, part of the Counter Ransomware Initiative, and leveraging the Financial Action Task Force (FATF) in its work on cryptocurrency, which is the primary source of ransom payments.58For information on the International Counter Ransomware Task Force, see https://counter-ransomware.org/aboutus. “Countering Ransomware Financing,” FATF, March 2023, https://www.fatf-gafi.org/content/dam/fatf-gafi/reports/Countering-Ransomware-Financing.pdf.coredownload.pdf. A coordinated effort might include Europol, Interpol, and some regional bodies as well as insurance associations and others. As specialist companies have developed to negotiate and facilitate ransom payments, some industry standards could be developed to require these companies to follow agreed practices in accordance with guidelines from FATF and others to ensure sanctions’ enforcement.
In the longer term, incident reporting might be expanded beyond ransomware. The Organization for Economic Cooperation and Development (OECD) has been very forward-thinking in developing an approach to define and monitor AI risks;59“Overview,” OECD AI Incidents Monitor: OECD AI, https://oecd.ai/en/incidents-methodology. This includes, for example, “severity, industry, related AI Principle, types of harms and affected stakeholders.” it is not too late to have centralized coordination around cyber risks.
Require More Consistent Minimum Conditions and Definitions for Coverage/Benefits
Re/insurers evaluate those to whom coverage is provided. How this process is managed is critical to both industry health and capacity as well as incentive structures for insurance clients and for insurers. Within the industry, some guidelines/standards have been set for coverage clauses to better manage risks and operating losses and to better attract reinsurers for risk sharing and increased capacity. Whereas underwriters want to know a lot, applicants want to minimize the application process causing a competitive dynamic between customers and insurers that needs careful management. In other risk areas, some insurance service providers have forms the industry traditionally uses to provide quotes.60“ISO Forms, Rules, and Loss Costs,” Verisk, n.d., https://www.verisk.com/insurance/products/forms-rules-and-loss-costs/. Simply standardizing some of the questions and policy wording would be a welcome evolution of the cyber insurance market and would help buyers understand the risks they have and their coverage.61Some have suggested using technographic data. This standardization could be done by leveraging new technological approaches and AI.62For example, see: Steven Byerley, “Can scanning tech predict cyber claims?: New report finds external scanning can be a potent tool,” Insurance Business, June 30, 2023, https://www.insurancebusinessmag.com/us/news/cyber/can-scanning-tech-predict-cyber-claims-451152.aspx. Whether this approach could be agreed in the industry is an open question.
A critical issue is the imprecision in defining exclusions and limits, such as for war/warlike acts, attribution and its methods, what constitutes an impacted state, and what should be considered as a major impact. Lloyds has provided some guidance, but more questions persist on policy terms.63“Model State-Backed Cyber War Exclusion Clauses for Cyber Treaty Reinsurance,” Lloyd’s Market Association, March 1, 2024, https://www.lmalloyds.com/LMA_Bulletins/LMA24-011-CM.aspx; “Cyber war clauses,” Underwriting Team: Lloyd’s Market Association, https://www.lmalloyds.com/LMA/Underwriting/Non-Marine/Cyber_Clauses/cyber_war_clauses.aspx.
The issue of catastrophic losses from systemic risks looms large. A coordinated effort to explore and define the above terms within the context of systemic risks and how to manage them is needed, including identifying the elements of best practices for the insured. Those practices should change dynamically as technology and knowledge evolves. Increasing the liability of tech providers for their services/products will be an element of this effort. States should consider affording liability limits—or safe havens—to those following agreed good practices. Further, if some states decide to provide support to the insurance industry through a backstop that would cover some industry losses, then the states and stakeholders must clearly define the technical characteristics of systemic risks. This reality may obviate some complicated current policy requirements for political attribution and support the development of a coordinated effort toward some accountability.
Having an independent body determine attribution is something that the UN and historically the OECD have suggested. However, before that happens, the insurance industry needs guidance. Technical characterizations of systemic risks without the constraints of legal and political attribution could serve the industry well and help jump-start other international processes toward a robust, transparent, and accepted framework for accountability for supporting cyber norms.64Debra Decker, Andreas Kuehn, and Kathryn Rauhut, “Whodunit in Cyberspace: The Rocky Road from Attribution to Accountability,” Stimson Center, December 12, 2023, https://stimson.org/2023/whodunit-in-cyberspace-from-attribution-to-accountability/. See also: UN norms 13.f. and 13.g on not attacking but protecting critical infrastructure, at: UN Secretary General, “Group of Governmental Experts on Advancing Responsible State Behaviour in Cyberspace in the Context of International Security,” United Nations General Assembly, July 14, 2021, https://reachingcriticalwill.org/images/documents/Disarmament-fora/other/icts/gge/documents/gge-report-adopted.pdf.
Expand Understanding and Availability of Catastrophic Cyber Risk Mechanisms With Clear Terms in Backstops and Triggers
The insurance industry adapts to new risks, with some always willing to provide insurance where others may not and with new catastrophic risk instruments developing such as insurance-linked securities. As noted above, systemic risks are an inhibiting issue for insurers and reinsurers alike. As reinsurers attempt to manage their portfolio risk for cyber policies, and insured organizations continue to gain a better understanding of the exposure and potential for loss, there will continue to be a need for greater availability of capacity in the cyber insurance marketplace. To allow for expansion of capacity in the cyber insurance market, it will be necessary to expand the availability of mechanisms that allow insurers to better manage the potential of catastrophic cyber events. Currently, insurers have relatively limited options when it comes to managing catastrophic cyber risk, with most choosing to purchase reinsurance. In 2023, the market began to see some insurers pursue catastrophe bonds as an alternative to purely transferring risk to a reinsurer.65This includes so-called 144 bonds that allow for trading. See: “Rule 144A Catastrophe Bond,” Artemis, https://www.artemis.bm/glossary/rule-144a-catastrophe-bond/. Growing interest in ILS would allow insurers another opportunity to manage catastrophic risk through the issuance of securities whose performance is tied to the results of the underlying insurance portfolio.
The possible role of rating agencies in assessing re/insurers processes for managing risks and issuing policies needs to be further explored.66Julia Kagan, “Insurance Company Credit Rating: Overview and Examples,” Investopedia, last updated September 28, 2023, https://www.investopedia.com/terms/i/insurance-company-credit-rating.asp. With the advent of big data, rating agencies are expected to increasingly help drive better cybersecurity practices across industries,67Debra Decker, and Kathryn Rauhut, “Incentivizing Good Governance Beyond Regulatory Minimums,” Stimson Center, December 15, 2021, https://stimson.org/2021/incentivizing-good-governance-beyond-regulatory-minimums/. including within the insurance industry, as they rate ILS for the benefit of capital market investors.68For example, see: “Recent ILS Cyber Bond Issuance Encouraging for (Re)Insurers,” Fitch Ratings, January 31, 2023, https://www.fitchratings.com/research/insurance/recent-ils-cyber-bond-issuance-encouraging-for-re-insurers-31-01-2023
Market incentives such as insurance have a great untapped potential to strengthen cybersecurity norms and laws. These incentives just need to be further explored and harnessed.




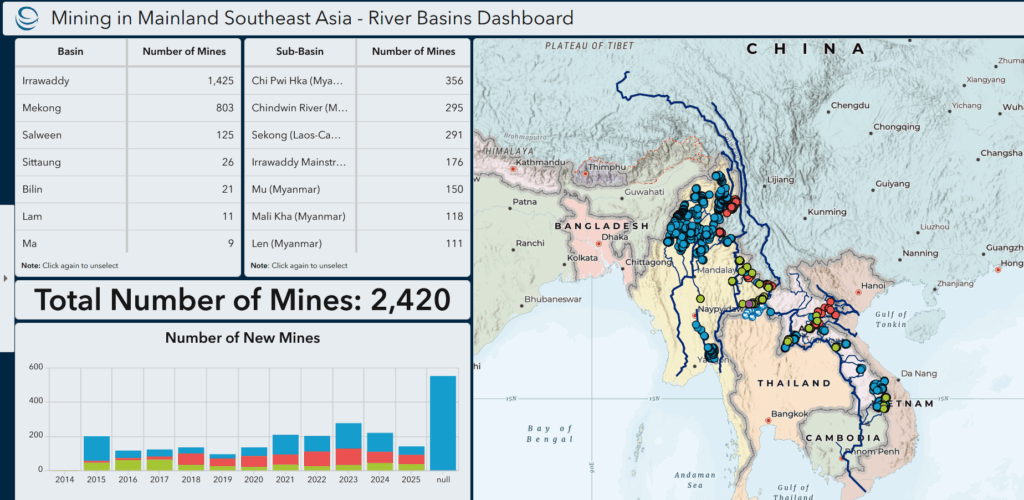




Current Geopolitics Shift Deep-Sea Mining Debates