First, I want to thank the Chair and the country of Singapore for all their work in this important area of cybersecurity. I also want to compliment the UN Institute for Disarmament Research for all the work it has done to support these efforts.
The Stimson Center is a 30-year-old Washington-based nonpartisan policy research center that works on international security issues. Let me start with just three aspects of our work that are applicable here.
First, we have extensively supported the UN, for example the work of the Security Council 1540 Committee. The 1540 Resolution calls for nonproliferation of weapons of mass destruction and their means of delivery. Cyber is a threat vector not unlike weapons of mass destruction.
Second, Stimson and the Hague Institute for Global Justice developed the Commission on Global Security, Justice and Governance, chaired by former UN Under Security General Ibrahim Gambari and former US Secretary of State Madeleine Albright, to consider new frameworks for collective action on critical issues. The Commission’s report, Crisis in Global Governance, has evolved into a platform today to foster dialogue and consensus around recommendations for the 2020 UN leaders’ Summit, including recommendations on cybersecurity. The initiative is called Just Security in an Ungoverned World.
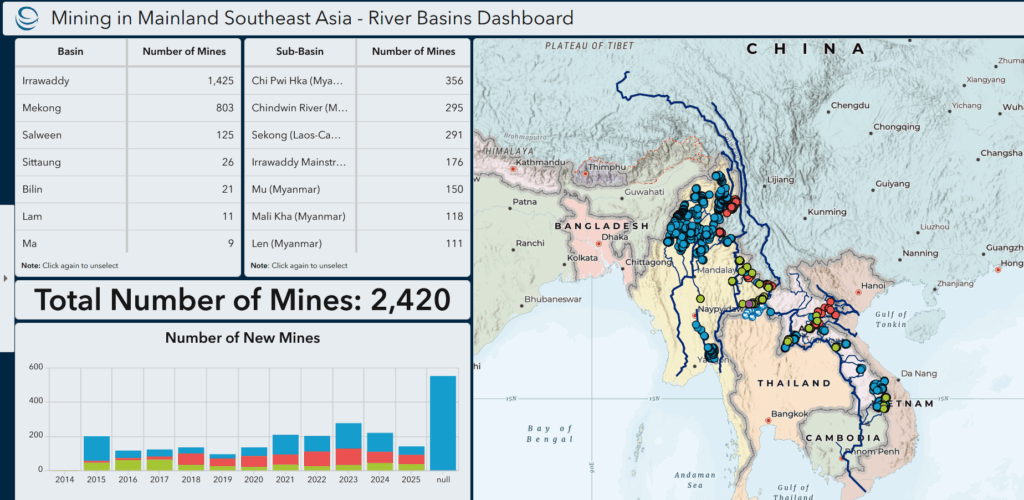
Lastly, I personally have also worked on cybersecurity issues specific to the civilian nuclear sector – in particular that and my work also with the International Atomic Energy Agency are what bring me here today. In international fora and many stakeholder discussions that we have held with regulators, insurers and cyber experts, we considered cyber risk and ways to address them. From this, we developed five proposals that are relevant to the work of the Open-ended Working Group. These proposals range from a regional pilot leveraging the Stimson Center’s work in SE Asia on mapping critical infrastructure to one on exploring regulatory requirements on and incentives for information disclosures on breaches and on system vulnerabilities, such as liability limitations for following agreed good practices.
But let me tell you about one project in particular that focuses on information-sharing and confidence-building measures. In this area, we do not have to start from scratch. We have lessons to be learned – what has worked and what has not worked – in information and norm development in other areas.
Recently, Stimson worked with the Japan Mission to the UN to put together a program for UN delegates looking at information sharing and accountability/attribution models. I want to thank Kaspersky, Microsoft, the Cyber Threat Alliance ad Palo Alto Networks for participating. At the discussions, we also showcased the nuclear security area. The co-chair of the Nuclear Forensics International Technical Working Group talked about this informal international association of individuals from technical scientists to law enforcement officials that have very effectively worked together to develop best practices and capacity and confidence in forensics and attribution – mainly through exercises and personal relationships developed over the last 10 years. There are laboratory specialists that become known for their specific forensic expertise – could we develop something similar in the cyber area? This is happening to some extent through the Global Forum on Cyber Expertise, but in the nuclear context the participants step out of their organizational affiliation and participate on individual levels. Some such as Trend Micro and Microsoft have talked about the need for accountability and ways to approach this. We can learn from other areas of international challenges.
Another example, very concretely, the 1540 Committee and its Expert Group developed an amazingly detailed matrix of hundreds of indicators that would help identify good compliance with the norms and intent of the 1540 resolution. This could be done for the norms defined in the earlier GGEs and similarly used for identifying gaps, as Mexico and other States have suggested. Stimson has put together a platform to help States match its 1540 needs to those who might help to fill those gaps in a prioritized way, whether they be States or organizations. This very systematic approach could be piloted for targeted capacity building in one or two regions.
In short, we can jumpstart and streamline efforts to reduce cyber risks by looking to what has worked or not in other areas, whether it be in Chem, Bio, Rad/Nuclear areas, or it could be deeper assessments of international experience in deterrence and accountability including in conventional warfare. Stakeholders who should be included in discussions on accountability, for example, are insurance companies – Zurich has denied a claim for cyber insurance payout on a business’ losses due to NotPetya because Zurich insurance says the losses fall under an exclusion for war-like acts.
I would be happy to further discuss Stimson’s past and proposed work in the cyber area. Stimson’s approach is collaborative. We work with other stakeholders from international organizations and States to industry and civil society in addressing complex issue areas. We have been awarded the MacArthur Foundation Award for being a creative and effective institution. Our work has been supported by many States and organizations. We would love to expand our work with Singapore and Switzerland and other States interested in exploring innovative, efficient approaches to managing cybersecurity risks.
Contact: Debra Decker, Senior Advisor, Stimson Center, [email protected]
For the UN General Assembly resolution establishing this OEWG, see: https://undocs.org/en/A/RES/73/27









Current Geopolitics Shift Deep-Sea Mining Debates