Origins, Progress, and Unfinished Business: NATO’s Protection of Civilians Policy

…become ingrained in training or planning for operations. Training and Education “Personnel training is the best protection we can offer civilian populations, hands down, bar none, full stop.”21Interview by author,…
Empowering Congress on the Korean Peninsula
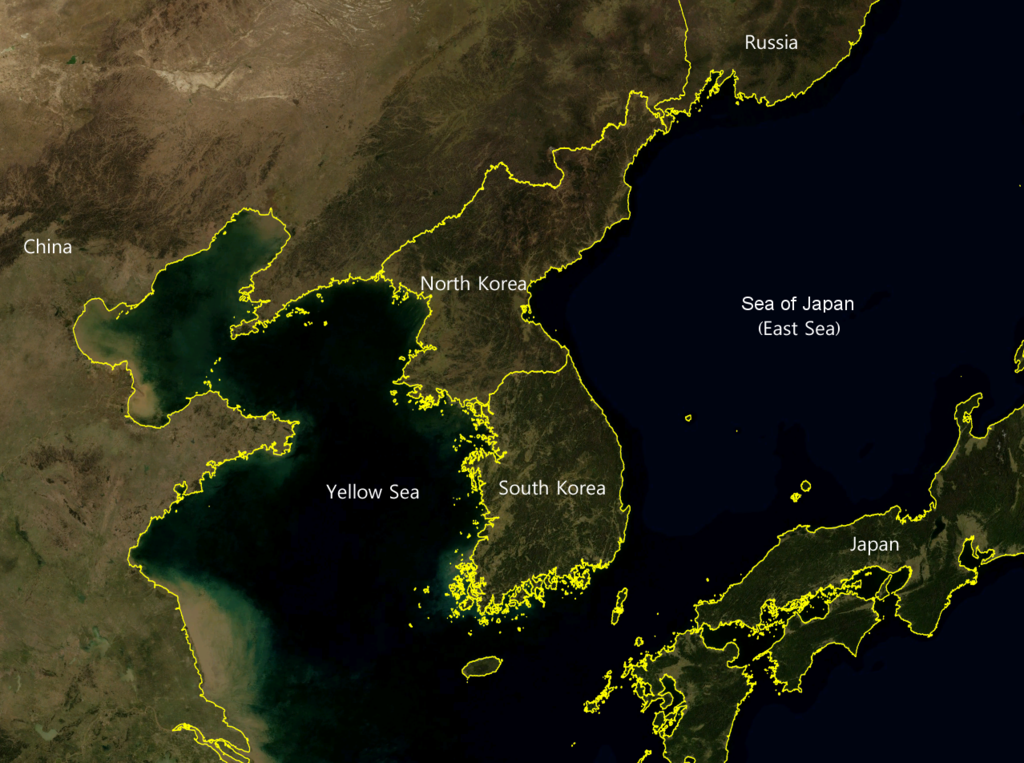
…Relations Committee and House Foreign Affairs Committee should do the same with the ROK’s Foreign Affairs and Unification Committee. Such interactions would assist staffers and lawmakers on either side to…
Military Coercion and US Foreign Policy: The Use of Force Short of War

Ed Note — This first chapter of Military Coercion and US Foreign Policy is excerpted for readers interested in the book. It is available for purchase from Amazon or directly…
Many Sanctions, Few Friends: Junta Grapples with its Grip on Power

…health, and infrastructure building…importers and exporters, any person or organizations using foreign banking services.” The sanctions, announced by the U.S. in June, targeted Myanma Foreign Trade Bank (MFTB) and Myanma…
Mekong-U.S. Partnership Track 1.5 Policy Dialogue on Countering Scam Operations

…industry. National governments should adopt and apply shared definitions in domestic legal and regulatory frameworks. International organizations, NGOs, and labor agencies should provide training to law enforcement and other frontline…
Red Cell: The Chimera of Technological Superiority

…to avoid similar analytic failures in the future—the project works to challenge assumptions, misperceptions, and groupthink with a view to encouraging alternative approaches to America’s foreign and national security policy…
Environmental Security News This Week
…As the world’s climate changes, communities are making adaptations like these to build resilience in a new climate reality. Google Earth Illuminates Crimes at Sea A new interactive map on…
China’s Activities In Southeast Asia And The Implications For U.S. Interests
…on dissidents, provoked a dispute that could cause Google to abandon the Chinese market, and hacked into U.S. government and private sector computer networks, apparently to gain access to high…
