
Background
The rapid pace and geographic breadth of technology innovation; the staggering volume of international trade; globalized business practices from outsourcing to off-shoring with intricate and oft times invisible supply-chains; and the inherent inability of governments to act at the speed of 21st-century commerce: these are but a few factors negatively influencing our ability to manage the lengthening global proliferation supply chain. The net result has been the global diffusion of weapons technologies to Iran, North Korea, and even potentially to ISIS and al-Qaeda. The practical inability of governments to monitor the volume of private transactions around the globe necessitates the advent of complementary new approaches that better match and ultimately defeat emerging avenues for proliferation.
The Threat
As the A.Q. Khan network demonstrated, committed proliferators have become expert at exploiting the seams of the global regulatory network to procure and transship their illicit wares. Increasingly, the sophistication and agility of these networks allow them to remain steps ahead of government regulators and investigators who are hampered by bureaucratic processes and the opacity of global supply chains. Lacking access to classified intelligence surrounding potentially bad actors, even well-intentioned firms are unable to conduct more thorough “know-your-customer” due diligence.
Our objective must be to prevent would-be bad actors from acquiring the technologies needed to build a nuclear device. Maximizing the capture of information on foreign entities seeking to purchase dual-use technologies or products from U.S. companies is an essential first step. In order to purchase dual-use technology or products from a U.S. company, foreign buyers must submit a request to the American company that, if acted upon, is then submitted to the Commerce Department and subjected to an interagency review before being either confirmed or denied by the Commerce Department, as illustrated below in Figure 1.
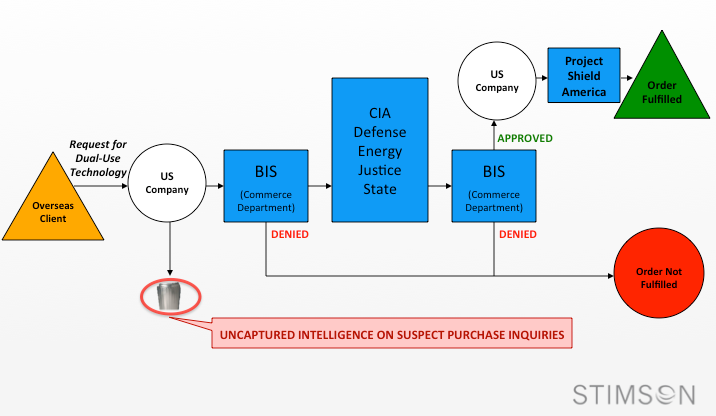
During the government review stage, each foreign request is vetted for possible connections to terrorist groups or other bad actors. When suspicious links are found, the Commerce Department can deny the request while other agencies scrub the request for valuable intelligence including, but certainly not limited to, which groups are seeking nuclear capabilities, how sophisticated their operations are, and their progress on the path to nuclear armaments.
The dangers posed by a nuclear-armed terrorist group, rogue states, or other bad actors necessitate constant vigilance and monitoring. The current system for handling requests for dual-use technologies, however, misses out on a valuable source of intelligence—the requests for dual-use technology that companies themselves consider too risky to even submit to the government for review. Because of the costs associated with such a submission, companies have no reason to file requests they are confident will be denied. Similarly, there currently exists no mechanism through which to incentivize companies to share even the most basic information about these requests, information that could contribute to national security and nonproliferation.
The Competition
To address this deficiency, the Stimson Center and NSquare held a challenge administered by InnoCentive that sought to build an information sharing solution backed by market-based incentives whereby private industry could identify and share suspect information. Such a mechanism can help governments disrupt foreign based individuals, corporations, terrorist groups or governments from acquiring U.S. technologies to build nuclear weapons of mass destruction by facilitating a technological platform through which anonymous information (uncaptured intelligence on suspect purchase inquiries) could be collected and shared. This challenge aims to establish a system whereby such information could be used: a) by other companies to help reduce the internal cost of due diligence necessary to research the legitimacy of overseas clients; and b) by the U.S. government to identify potential foreign proliferation networks.
The solutions solicited through this challenge focused on the mechanics, structure and operations of an information collection system that is low cost or no-cost for industry participants. The challenge further specified that the proposed platform should be capable of collecting data from a wide cross section of US industry actors, collating that information, and returning anonymized data on suspicious foreign clients that would allow individual companies to better assess whether or not to make a sale. All solutions were requested to contribute both to US national security and to industry profit motives by helping both actors to identify and prevent the sale of sensitive knowledge and goods to bad actors.
To measure the success of the proposed solutions, the challenge stipulated that the solutions achieve the following goals within two years:
- The existence of an electronic platform capable of receiving information from US private companies about suspect requests for information or products;
- The participation of a wide range of US firms whose technologies could be diverted for nefarious purposes (the development of nuclear weapons);
- The adoption and management of this platform by a trusted US industry association;
- Built-in incentives for private companies to provide information into this platform that could include the ability to pulse the platform for information and compare against pending sales requests from abroad; and
- The ability to share anonymous tips to US government authorities for further investigation.
Proposed solutions to the issues outlined in this challenge differed in methodology and scope, often testing the limits and requirements of the challenge itself. The following section details the recurring themes from these solutions, and evaluates their application to the problem at hand.
Proposed Solutions
The following mechanisms were drawn from the solutions submitted in response to the challenge set forth by the Stimson Center and N Square. It is important to note that these mechanisms are neither mutually exclusive nor do they each purport to address all facets of the challenge. Indeed, it is when these mechanisms are considered in the context of a larger whole that they would be most effective. For this reason, an outline for the synthesis of these mechanisms will follow their individual descriptions:
- Blockchain Infrastructure: A number of the proposed solutions recommended the use of block chain infrastructure to anonymize and protect data, ensuring that cooperation in a system to identify and catalogue suspicious actors is not harmful to participating parties. The concept of a blockchain, a distributed database that continuously records the contribution and alteration of data while being secured from tampering and revision, was proposed as a method of reporting suspicious requests or transactions by companies that produce dual use technology in exchange for a reward to be paid in cryptocurrency. Such a database, however, is of limited utility due to its distributed nature, which makes the primary control of the database by an industry association or government agency impossible. Moreover, the proposals that emphasized blockchain infrastructure focused on whistleblowers within companies that take issue with orders that have gone through or, at the very least, been submitted to the government for review. This means that the information that they would be providing under those proposals is already in government hands and, therefore, not the information targeted by this challenge. Even so, the blockchain proposals emphasized factors central to the success of any mechanism designed to address the challenge at hand, namely the importance of contributors’ privacy and database security.
- Artificial Intelligence: The use of artificial intelligence (A.I.) or algorithms applied to international corporate transactions was proposed as a means to minimize the human role in the reporting process. This solution proposed that, incoming orders be automatically cross-referenced with a list of bad actors, with orders from such actors flagged for the company and forwarded to the relevant authority. This proposal specified that, in order to minimize the fear that the government would retain alternative methods of viewing companies’ data, the necessary A.I. or algorithms should be created by a reputable company with a history of standing up for companies’ right to privacy. This proposal is inherently limited, however, by the fact that A.I. and algorithms such as those included in this entry can only interact with an existing database of bad actors. While this may improve the efficiency of the private sector in conducting due diligence, it does not provide for the capture of additional information and is of limited utility to government agencies. Nonetheless, the application of A.I clearly has a growing role as the volume and complexity of the global supply chain expands.
- Self-recording: Another proposal recommended self-recording, or the collecting of information on incoming or suspicious orders through automatic processes rather than voluntary submission. This solution is largely in line with proposals for the use of algorithms or A.I. but differs in that it transmits more complete information regarding incoming orders to a database that can be accessed by government industry personnel as well as the participating companies. Essentially, the database would compile a request history across a specific industry, learning which buyers’ requests are likely to approved versus discarded or denied. In effect, access to this history would ease the due diligence burden placed on companies by allowing them to compare a buyer’s request with their history of working with U.S. companies. Furthermore, since a company’s discretion in submitting accounts to the database is removed via the automatic process, making the information in the database more complete, to the benefit of the public and private sectors.
- Procurement Responsibility Index: Another proposal called for the creation of a Procurement Responsibility Index (PRI) to grade buyers on the percentage of completed orders per attempts to purchase dual use items. The PRI includes instances where companies tossed out their requests because of their suspicious nature as well as instances when government agencies blocked the sale. By ranking buyers by what is effectively the conversion rate of effort on the part of the seller to sales, companies would be incentivized to work with trustworthy companies both in terms of profit for the company and responsibility in terms of nonproliferation.
- Geospatial Reporting: Further proposals suggested using geospatial reporting to link purchases from seemingly different companies that were requesting deliveries to the same or similar destinations. This allows for a more nuanced approach that calculates a buyers’ PRI by providing context for the buyer’s request. If state-owned corporation A has purchased half of the components for a rudimentary nuclear device and shipped them to an area in which state-owned company B then wants to ship the remaining components, this should raise suspicions about the intent and reliability of those companies. This information, independent of its current availability to government agencies, would allow companies to be more responsible in their transfers, behavior that would be incentivized by the desire to avoid doing business with entities that would be under either investigation or threat of impending sanctions.
Taken individually, none of these mechanisms can succeed in fulfilling the challenge’s requirement to build an information sharing solution backed by market-based incentives whereby private industry could identify and share suspect information that can help governments disrupt foreign based individuals, corporations, terrorist groups or governments from acquiring U.S. technologies to build nuclear weapons of mass destruction. The possible combination of these mechanisms, however, provides avenues by which the initial goals of the challenge can be attained.
These ideas demonstrate that by tapping the technology sector, innovative new ideas can be generated to address challenges that the national security community has struggled to manage for decades—including the threat posed by nuclear weapons.
N Square is a multimillion dollar initiative designed to stimulate innovation in the fields of nuclear disarmament, nonproliferation and safety and security. N Square is the brainchild of The Carnegie Corporation of New York, the William and Flora Hewlett Foundation, the John D. and Catherine T. MacArthur Foundation, the Ploughshares Fund, and the Skoll Global Threats Fund. N Square is based on the idea that new forms of cross-sector collaboration—combined with the sheer ingenuity of an engaged public—will enable us to innovate our way to a world free from the risks associated with nuclear weapons and fissile materials.
